IT Support & Managed Services for Windhoek and Namibia Businesses — Secure, Fast, Reliable
share, collaborate and communicate across organizational boundaries.
- Windhoek
- Rehoboth
- Okahandja
- Otjiwarongo
- Swakopmund
- Walvisbay
- Grootfontein
- Gobabis
Anywhere

We Help Small & Growing
Businesses in Windhoek
If you have:
5–50 employees
Microsoft 365
Servers or shared drives
Network & WiFi infrastructure
No full-time IT staff
We act as your outsourced IT department.

WOMAN IN TECH
We encourage and empower woman in tech.
Many woman in our communities are eager to
voice their hunger for IT and we believe with the
right tools and assistance we might get their
voices heard.

EFFECTIVE HOME AND OFFICE ITSUPPORT AND MAINTENANCE
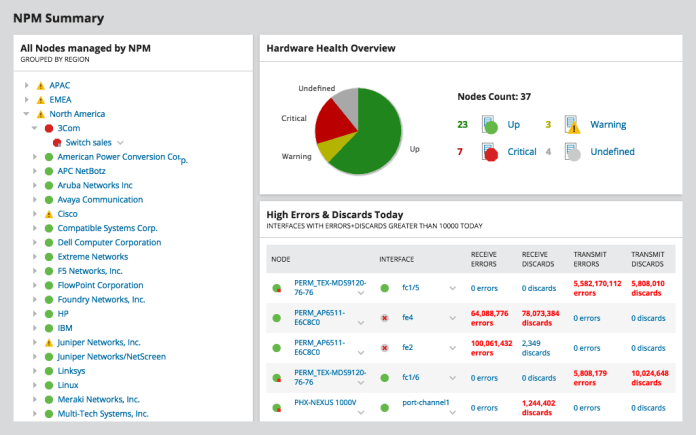
✔ Less downtime for your business
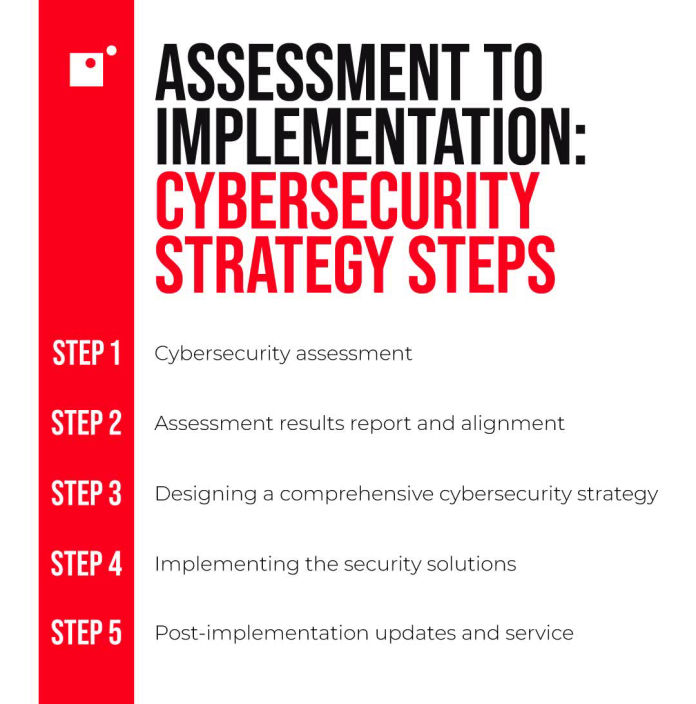
✔ Better cybersecurity protection
✔ Quick response when servers fail
✔ No need to hire a full-time IT staff
DID YOU BACKUP TODAY
DATA PROTECTION
#WorldBackupDay, 31 March 2026.
#StaySecure